LTE FDD vs TDD: Key Differences Explained
Advertisement
LTE (Long Term Evolution) has revolutionized mobile communication, offering high-speed data connectivity across the globe. Two major duplexing methods in LTE are Frequency Division Duplexing (FDD) and Time Division Duplexing (TDD). While both are integral to LTE networks, they differ significantly in design, functionality, and use cases. This article dives deep into LTE FDD and TDD, comparing their strengths, weaknesses, and the scenarios where each excels.
TDD and FDD are two topologies by which critical resources, time and frequency, are shared among mobile subscribers or terminals. LTE uses both of these flavors to provide facility for the mobile subscribers or UEs (User Equipments) to utilize the scarce resource efficiently based on the need.
Let’s understand LTE FDD and TDD LTE versions with figures and band examples below. LTE has a radio frame of duration 10ms consisting of 10 subframes. Each subframe has two slots. The slot is of 0.5ms duration. Hence there are a total of 20 slots in a radio frame.
LTE FDD
In LTE, a base station is referred to as an eNodeB and a mobile subscriber is referred to as a UE.
Figure 1 describes the LTE FDD scenario. As shown in the figure, f1 and f2 are one pair of frequencies allocated separately for both the uplink and downlink direction.
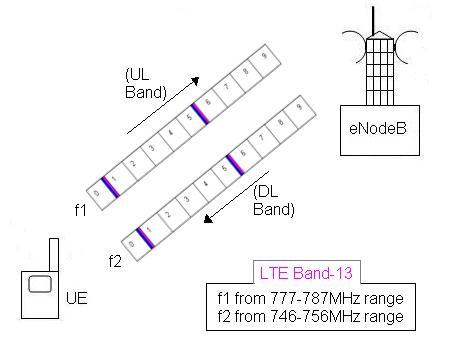
The figure mentions LTE band-13 with an uplink frequency of range 777 to 787MHz and a downlink frequency of range 746 to 756 MHz. Hence, f1 is allocated from the uplink band and f2 is allocated from the downlink frequency band. The entire radio frame of 10ms is used simultaneously over downlink and uplink directions.
Please note that downlink always refers to transmission from LTE eNodeB to UEs and uplink refers to transmission from UEs to eNodeB.
Both uplink and downlink will have 10MHz bandwidth each on which the entire frame will be used.
Advantages of LTE FDD
- Superior Coverage: FDD uses paired frequency bands, enabling it to provide wide-area coverage and consistent performance, especially in rural areas.
- Low Latency: With simultaneous transmission and reception, FDD ensures minimal latency, making it ideal for real-time applications like voice and video calls.
- Compatibility: FDD is widely adopted and compatible with existing 2G and 3G systems, simplifying integration and global roaming.
Disadvantages of LTE FDD
- Spectrum Usage: Requires paired spectrum bands, which can be costly and less efficient in terms of spectrum utilization.
- High Cost: The need for dedicated spectrum pairs increases the deployment cost, making it less attractive for operators with limited budgets.
- Less Flexibility: FDD’s rigid pairing structure limits its adaptability to varying traffic demands.
TDD LTE
Figure 2 describes the TDD LTE scenario. As shown in the figure, both uplink and downlink have been allocated the same frequency f1, but both use different time slots for mapping their information data.
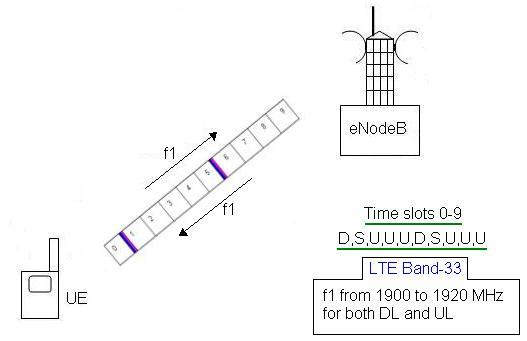
The figure mentions LTE band-33 which is from frequency 1900 to 1920MHz. The entire bandwidth of 20MHz is used for both eNodeB and UEs.
The figure mentions configuration of radio frame time slots 0 to 9 for UL/DL configuration of zero and 5ms DL/UL switch point periodicity. It is D,S,U,U,U,D,S,U,U,U.
Here, D stands for downlink and U stands for uplink. Hence, the subframes of the entire radio frame are divided and used for both the uplink and downlink direction.
Leading chipset manufacturers such as Ericsson, Altair semiconductor, and Qualcomm support both TDD and FDD versions of LTE on a single chip.
Advantages of LTE TDD
- Efficient Spectrum Use: TDD operates on a single unpaired band, allowing for more efficient spectrum utilization.
- Cost-Effective: With no need for paired spectrum, TDD reduces spectrum acquisition and deployment costs.
- Flexibility: TDD adapts dynamically to asymmetric data traffic, allocating more time slots to either upload or download as needed.
Disadvantages of LTE TDD
- Interference Issues: TDD can face interference challenges, especially when deployed in adjacent cells with different configurations.
- Limited Coverage: TDD’s reliance on time-based duplexing often results in shorter coverage compared to FDD.
- Latency: TDD’s sequential transmission and reception introduce higher latency, which may affect real-time applications.
Comparison between LTE FDD and TDD
The following table summarizes LTE FDD vs TDD versions. It compares both with respect to application, frame structure, Guard period, frequency band, interference, data rate, and interoperability with other RATs (Radio Access Technologies).
| Aspect | LTE FDD | TDD LTE |
|---|---|---|
| Spectrum Usage | Requires paired frequency bands (uplink and downlink). | Operates on a single unpaired frequency band. |
| Transmission Mode | Simultaneous uplink and downlink on separate frequencies. | Alternates uplink and downlink in time slots. |
| Efficiency | Less spectrum efficient due to dedicated pairing. | More spectrum efficient with dynamic allocation. |
| Coverage | Provides wider coverage, especially in rural areas. | Offers shorter coverage, suitable for urban areas. |
| Latency | Lower latency due to simultaneous data transfer. | Higher latency due to sequential data transfer. |
| Interference | Less prone to interference between adjacent cells. | More susceptible to interference in adjacent cells. |
| Cost | Higher deployment cost due to paired spectrum needs. | Lower cost as it uses unpaired spectrum. |
| Traffic Suitability | Better suited for symmetric traffic (equal uplink and downlink). | Ideal for asymmetric traffic (e.g., more downlink demand). |
| Adoption | Widely used and globally supported, including rural areas. | Primarily used in densely populated urban areas. |
| Application | FDD version is used where both uplink and downlink data rates are symmetrical. | TDD version is used where both uplink and downlink data rates are asymmetrical. |
| Frame structure | Uses FDD frame structure | Uses TDD frame structure |
| Guard periods | Not provided, every downlink subframe can be associated with an uplink subframe. | Provided in the center of special subframes and used for the advance of the uplink transmission timing. The no. of downlink and uplink subframes is different. |
| Frequency bands | REFER LTE Frequency Bands for FDD frequency ranges | REFER LTE Frequency Bands for TDD frequency ranges |
| Working with other RATs | Interference will be higher than TD version | TDD LTE works well with minimum interference along with TD-SCDMA RAT |
Both LTE FDD and TDD versions have their own applications and the same can be exploited by telecom operators based on traffic and other requirements.
Conclusion
Choosing between LTE FDD and TDD depends on the specific requirements of your network, including spectrum availability, cost considerations, and user demand. FDD excels in wide coverage and consistent performance, making it ideal for rural areas. TDD, with its flexibility and cost efficiency, suits urban environments and asymmetric data traffic. Understanding their differences ensures optimal deployment and improved network efficiency.
Advertisement
 RF
RF




