ARP Attack Types: MAC Flooding and ARP Spoofing Explained
Advertisement
This article covers the basics of ARP attacks, including MAC flooding and ARP spoofing (also known as ARP poisoning). It also discusses prevention techniques for MAC flooding and ARP spoofing.
What is ARP (Address Resolution Protocol)?
ARP operates at Layer 2, the data link layer, of the OSI model. Its primary function is to resolve IP addresses to their corresponding MAC addresses (physical addresses). In essence, it translates a logical address (IP) into a physical address (MAC) so that data can be sent to the correct device on a local network.
To participate in internet communication, every device needs a unique MAC address. There is a reverse protocol called RARP (Reverse Address Resolution Protocol), which converts MAC addresses back into IP addresses, although it’s less commonly used now.
How ARP Protocol Works
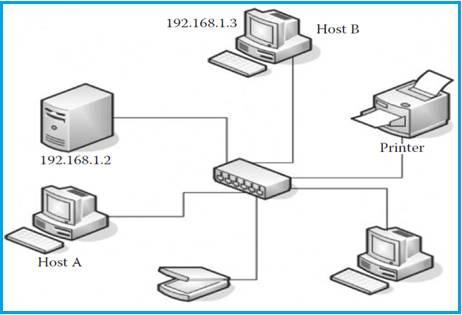
Let’s understand how ARP works using the example network in the figure. Suppose Host A needs to communicate with Host B. To do this, Host A needs Host B’s MAC address.
-
ARP Table Check: Host A first checks its ARP table (a cache of IP-to-MAC address mappings) to see if it already knows the MAC address associated with Host B’s IP address (192.168.1.3).
-
Direct Communication (if found): If the MAC address is in the ARP table, Host A and Host B can communicate directly.
-
ARP Request (if not found): If the MAC address is not in the ARP table, Host A broadcasts an “ARP request” message to all devices on the local network. This request contains the destination IP address (192.168.1.3) and a broadcast MAC address (all zeros).
-
ARP Response: The device whose IP address matches the destination IP address in the ARP request (in this case, Host B) will send an “ARP response” back to Host A. This response contains Host B’s MAC address along with its IP address (192.168.1.3).
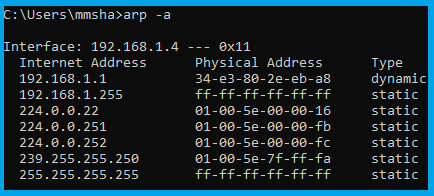
The above table is referred to as the ARP table or CAM (Content Addressable Memory) table. It contains internet addresses (IP addresses) and physical address entries of all connected systems. You can check this table by issuing the arp -a command in the command prompt.
ARP Attack Types
Hackers can obtain details about their desired systems through network and system sniffing. Network sniffing mainly comes in two forms: active sniffing and passive sniffing.
In active sniffing , the hacker directly communicates with the target system by sending packets or requests. ARP attack types, such as MAC flooding and ARP spoofing/poisoning, fall under the active sniffing category.
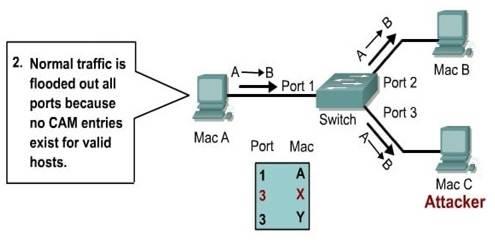
MAC Flooding
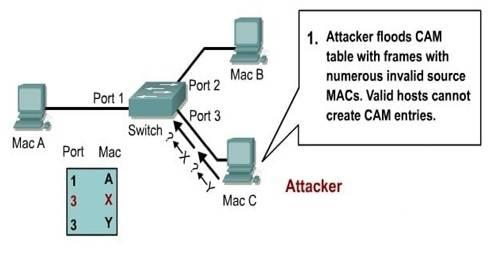
MAC flooding is the process of overwhelming a switch’s CAM table by sending a large number of ARP replies to it. When the switch’s CAM table becomes full, it effectively enters “hub mode.” In hub mode, the switch forwards all traffic to every connected computer on the network. As a result, an attacker can capture all network traffic using sniffing software.
- The “Macof” tool can be used to rapidly fill the CAM table of a target switch. It achieves this by sending a large number of MAC address entries per minute. To do this, you run the
Macofcommand in the terminal. - Once the CAM table is flooded, a tool like Wireshark can be used to capture the network traffic in promiscuous mode.
ARP Spoofing | ARP Poisoning
This type of ARP attack is used to intercept network traffic by positioning the attacker in the middle of a communication link. This is accomplished using fake ARP replies.
The ARP protocol assumes that an ARP response comes from the legitimate terminal whose IP address matches the one contained in the ARP request message. Crucially, there is no built-in mechanism to validate whether an ARP response was actually sent from the correct device. Hackers exploit this design flaw.
In ARP spoofing, the attacker sends spoofed ARP responses to a computer on the network, making it believe that a certain IP address is associated with the attacker’s MAC address. This allows the attacker to poison the ARP cache or ARP table, which tracks IP-to-MAC address mappings. This is why it’s also known as ARP poisoning.
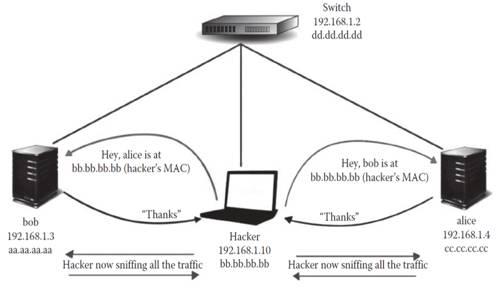
The figure depicts how a hacker can capture traffic flowing between Bob and Alice. To perform ARP spoofing, the hacker sends two ARP responses: one to Bob and the other to Alice, both containing the attacker’s MAC address.
Advertisement
 RF
RF






