Active vs. Passive Network Sniffing: Key Differences Explained
Advertisement
Network sniffing, a form of eavesdropping, involves monitoring and capturing data packets traveling across network. It is often used with the intent of intercepting unencrypted credentials. It can be categorized into active sniffing and passive sniffing, depending on whether the network is interfered with during monitoring. Understanding the differences between these methods is crucial for identifying vulnerabilities and ensuring secure network communication.
What is Network Sniffing?
Network sniffing is a type of attack where an attacker intercepts data packets traversing a wired or wireless network. It’s essentially electronic eavesdropping. The primary goal is often to capture unencrypted usernames, passwords, and other sensitive information.
Common protocols vulnerable to sniffing attacks include FTP, HTTP, SMTP, NNTP, POP, IMAP, TELNET etc.
The most effective defense against sniffing is to use encrypted protocols, making it significantly harder to decipher captured traffic.
As mentioned, it can be broadly classified into two main categories viz. active and passive sniffing.
Active Sniffing
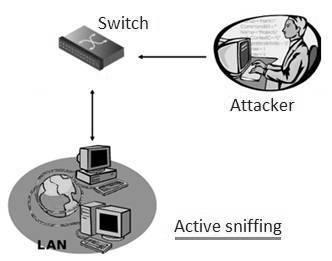
- In active sniffing, the attacker directly interacts with the target machine. They send packets to the target and analyze the responses.
- Active sniffing typically occurs in switched networks. The attacker attempts to “poison” the switch by flooding it with bogus MAC addresses.
Examples of Active Sniffing:
- ARP Spoofing
- MAC Flooding
- HTTPS and SSH Spoofing
- DNS Spoofing
Passive Sniffing
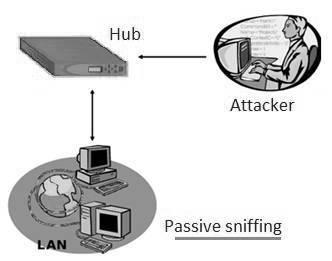
- In passive sniffing, the attacker doesn’t interact directly with the target. They simply “listen” to network traffic, capturing packets transmitted and received by the network or exchanged between two machines.
- Passive sniffing commonly occurs in hub-based networks. The attacker connects to the hub from their machine. An attacker typically needs an account on the LAN.
Examples of Passive Sniffing:
- Hub-based Networks
- Wireless Networks
Conclusion
Active sniffing involves interacting with the network to capture traffic, making it easier to detect but effective on switched networks, while passive sniffing silently listens to network traffic without interference, making it harder to detect. Both techniques are vital in ethical hacking and cybersecurity auditing, but they differ significantly in their approach and detectability.
Advertisement
 RF
RF





