Cloud Security: 10 Advantages and Disadvantages
Advertisement
Cloud security has become a cornerstone for modern businesses as they increasingly rely on cloud based solutions for data storage, processing, and collaboration. While cloud security offers numerous benefits, such as scalability and advanced protection measures, it also presents certain challenges, including dependency on providers and potential vulnerabilities. This guide provides an in-depth analysis of the advantages and disadvantages of cloud security to help organizations make informed decisions about safeguarding their digital assets.
What is Cloud Security?
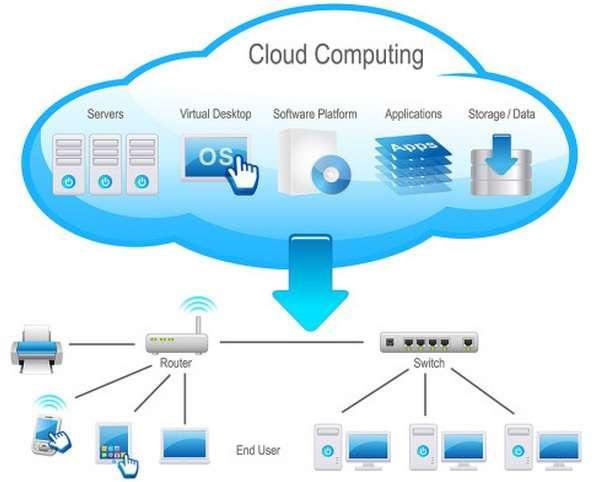
The cloud computing model consists of two parts: cloud service providers and end users. There are three deployment models: public, private, and hybrid. The cloud services delivery models are SaaS, PaaS, and IaaS.
When business enterprises move their computing environments with their identities, information, and infrastructure to the cloud, they compromise some level of control. This leads to security threats. It has become essential to have security assurances from cloud providers and also to have secured processes and events. The cloud security principles comprise three categories: identity, information, and infrastructure. Some of the security concerns are loss of data, account seizing, service traffic hindrance, and vulnerable APIs.
The solution for cloud security should provide protection from theft, leakage, and deletion by adopting security policies.
The cloud infrastructure should be secure irrespective of the deployment model (i.e., public or private) and whether the service is SaaS, PaaS, or IaaS. Here, SaaS refers to Software as a Service, PaaS refers to Platform as a Service, and IaaS refers to Infrastructure as a Service.
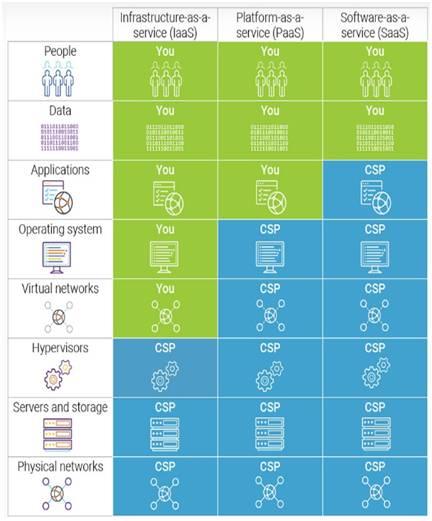
The figure depicts a shared responsibility model of cloud security. Here, it’s the joint responsibility of users and cloud providers to deliver a secured cloud computing model. Infrastructure security can be viewed, assessed, and implemented according to its building levels such as network, host, and application levels.
In the figure, “YOU” stands for Customer or user, whereas “CSP” stands for Cloud Service Provider. It shows various resources (e.g., data, applications, OS, networks, servers, storage, etc.) and their responsibility map.
- The network level security ensures confidentiality and integrity of data in transit to/from a public cloud provider. It also ensures proper access control.
- The host level security considers deployment models (i.e., public, private, or hybrid) and cloud services delivery models (SaaS, PaaS, or IaaS). At PaaS and SaaS, the operating system is hidden from end users. IaaS customers will have a potential threat on hypervisors.
- Application-level security depends on single-user apps or multi-user apps.
- Data security includes data privacy, data protection, data availability, data location, and its secure transmission. The data security can be achieved through identity management, encryption, and access control. IAM (Identity and Access Management) is a branch of cloud security that allows legitimate persons to retrieve legitimate resources at the legitimate time for legitimate reasons.
Advantages of Cloud Security
Following are some of the benefits of Cloud security:
- Scalability: Cloud security solutions can easily scale with your organization’s growth, ensuring consistent protection across expanding resources.
- Cost Efficiency: Reduces the need for on-premises security infrastructure, lowering initial setup and maintenance costs.
- Accessibility: Allows secure access to data and applications from anywhere, enabling remote work and flexibility.
- Advanced Threat Detection: Utilizes AI and machine learning for real-time monitoring and advanced threat prevention.
- Automatic Updates: Ensures the latest security measures are always in place through automatic updates and patches.
- Disaster Recovery: Provides robust backup and recovery solutions to minimize downtime and data loss during incidents.
- Compliance: Helps businesses meet regulatory and compliance requirements with pre-built frameworks.
- Shared Responsibility: Delegates certain security responsibilities to cloud providers, reducing the internal IT burden.
- High Availability: Ensures consistent uptime and secure access to data, even during peak loads or system failures.
- Centralized Management: Offers unified dashboards to monitor and manage security policies across all cloud environments.
Disadvantages of Cloud Security
Following are some of the drawbacks of Cloud security:
- Data Breaches: Despite strong measures, cloud environments are still vulnerable to data breaches if improperly managed.
- Lack of Control: Organizations rely on third-party providers, which can limit direct control over security measures.
- Service Downtime: Cloud providers’ outages can disrupt security monitoring and access to critical data.
- Insider Threats: Employees or administrators with malicious intent can exploit cloud systems.
- Compliance Complexity: Navigating varying data protection regulations across regions can be challenging.
- Shared Environment Risks: Multitenancy in the cloud can lead to cross-contamination of data if isolation isn’t maintained.
- Cost Overruns: Over time, scaling security services can lead to unforeseen expenses if not monitored.
- Limited Customization: Pre-built security frameworks may not cater to specific organizational needs.
- Latency Issues: Security checks in the cloud can introduce latency, affecting application performance.
- Dependence on Internet Connectivity: Requires stable internet connections; disruptions can impact security operations.
Conclusion : Cloud security offers significant benefits, including enhanced data protection, cost efficiency and scalability. However, organizations must be aware of its limitations, such as reliance on third-party providers and possible security risks. By carefully weighing the advantages and disadvantages, businesses can implement effective strategies to maximize the benefits of cloud security while mitigating its challenges, ensuring a robust and secure digital environment.
Advertisement
 RF
RF








