WirelessHART vs. ISA100.11a: A Comprehensive Comparison
Advertisement
This article explores the differences and similarities between WirelessHART and ISA100.11a, two prominent wireless technologies. Both are based on the IEEE 802.15.4-2006 standard and operate in the 2.4 GHz frequency band, making them suitable for applications like process automation and plant automation, essentially functioning as low-rate wireless personal area networks.
Interestingly, ISA100.11a uses a MAC layer that’s a modified version of the MAC layer used by WirelessHART. They also share a similar mechanism for data transport to and from the gateway. Thanks to their low power consumption, devices using these technologies can enjoy extended battery life.
To avoid interference, the radio employs channel hopping and DSSS (Direct-Sequence Spread Spectrum) techniques, allowing them to coexist peacefully within the same frequency spectrum.
WirelessHART
Here are some key features of WirelessHART technology:
- It uses a TDMA/CSMA (Time Division Multiple Access/Carrier Sense Multiple Access) based wireless mesh networking approach.
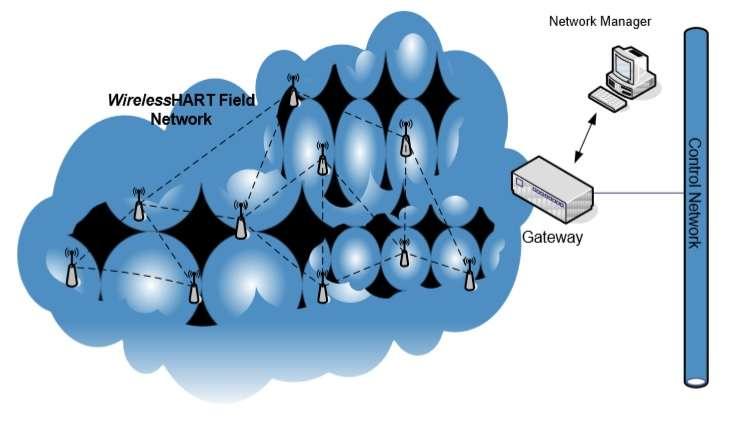
- A WirelessHART network typically includes field devices, a gateway, a network manager, a security manager, and handheld devices.
- It uses 16 channels in the 2.4 GHz band, with a 5 MHz gap between each channel.
- It supports 128-bit AES encryption for secure communication.
Refer to this article for more on WirelessHART basics.
ISA100.11a Wireless
Key features of ISA100.11a Wireless technology include:
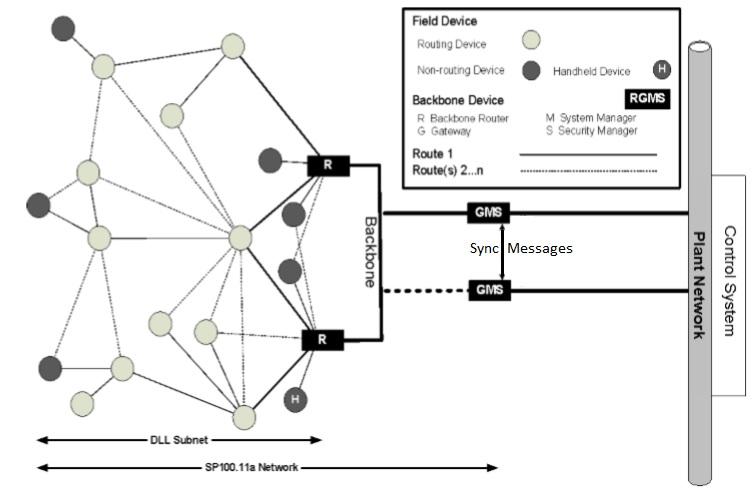
- The network comprises field devices (handheld, I/O devices like sensors and actuators), backbone routers, a gateway, a system manager, and a security manager.
- It supports the IPv6 protocol, leveraging its benefits.
- It can operate in star, mesh, and star-mesh topologies.
- It uses TDMA/CSMA for both communication and resource sharing.
Refer to this tutorial for a deeper dive into ISA100.11a Wireless.
WirelessHART vs. ISA100.11a: A Detailed Comparison
The following table compares WirelessHART and ISA100.11a, highlighting their similarities and differences:
| Feature of Comparison | WirelessHART | ISA100.11a |
|---|---|---|
| Architecture level | Network Access Points; Peer-to-peer communication with potential security risks | Backbone device; Provisioning device; Well-defined security manager; Subnet definition; Contract provides QoS for device communication |
| Digital Link Layer | One channel hopping scheme; Passive neighbor discovery; Fixed timeslot | Three channel hopping schemes; Active and passive neighbor discovery; Subnet routing; Configurable length of timeslot |
| Network layer | Only one header specification; End-to-end session security; Based on HART addressing | Three header specifications; Fragmentation and assembly; Based on IPv6 addressing; Compatible with 6LoWPAN |
| Transport layer | TCP-like reliable communication service | Connectionless service (UDP); End-to-end session security; Compatibility of 6LoWPAN |
| Application layer | Command-orientation; Predefined data types; Support HART protocol | Object-Orientation; Standard management objects, industry-dependent/independent objects, and ASL services; Three communication interaction models; Support legacy protocol tunneling |
| Joining Process | Only symmetric method | Symmetric and asymmetric methods; Symmetric and asymmetric key agreement during the key distribution scheme |
| Provisioning Process | Cable connection to the maintenance port using Handheld | OTA symmetric and asymmetric methods; Out-of-Band methods |
Advertisement
 RF
RF


