IaaS: Advantages and Disadvantages of Infrastructure as a Service
Advertisement
This page explores the advantages and disadvantages of Infrastructure as a Service (IaaS) and provides a basic overview.
What is IaaS?
Introduction: IaaS enables businesses or individual users to run applications on a cloud provider’s hardware. It facilitates the migration of applications to the provider’s infrastructure, allowing suppliers to share physical servers with users.
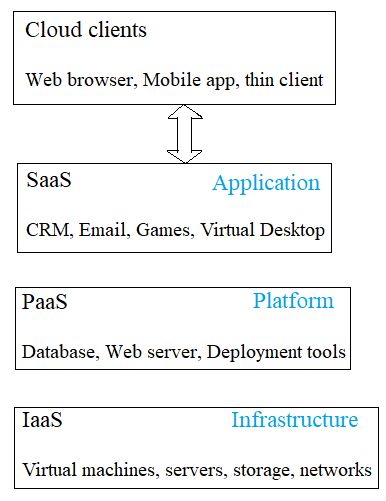
IaaS types include private cloud, dedicated hosting, hybrid hosting, and cloud hosting.
Figure 1 (below) illustrates common tasks performed by IaaS. IaaS provides access to fundamental resources like physical machines, virtual machines, and virtual storage.
Besides these resources, IaaS also offers:
- Virtual machine disk storage
- Virtual Local Area Networks (VLANs)
- Load Balancers
- IP Addresses
- Software bundles
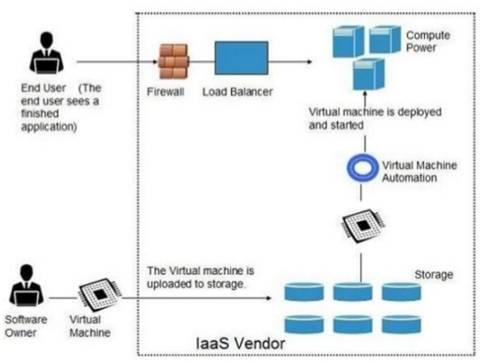
All the resources mentioned above are made available to end users via server virtualization. Users or customers can leverage these resources as if they own them.
Examples of IaaS vendors:
- Amazon Web Services
- OpSource
- NTT Communications
- GoGrid
- Terremark
- Blizzard
- AT&T
- Rackspace
Benefits or Advantages of IaaS
The following are the benefits or advantages of IaaS:
- Full Control: It allows full control of computing resources through administrative access to VMs (Virtual Machines). Customers can run any application, automate provisioning, or build their own VM.
- Flexible and Efficient: It offers flexible and efficient renting of computer hardware.
- Portability and Interoperability: It provides portability and interoperability with legacy applications.
- Simplified Integration: It simplifies integration with enterprise infrastructure.
- Reduced Costs and Maintenance: Customers do not have to worry about the cost and maintenance of running their own virtual infrastructure (instead of their own hardware).
Drawbacks or Disadvantages of IaaS
The following are the drawbacks or disadvantages of IaaS:
- Cost: It can be the most expensive service as the customer is essentially leasing a tangible resource. The provider can charge for every cycle, bit of RAM, or disk space used.
- Customer Responsibility: Customers are responsible for backups and all other aspects of VM management.
- Limited Server Control: Customers or users do not have direct control over the specific server used or its geographical location.
- Security Vulnerabilities: Compatibility issues with legacy security vulnerabilities can arise.
- Virtual Machine Sprawl: Potential for uncontrolled growth and management complexities of virtual machines.
- Data Erase Practices: Concerns regarding data erasure practices of the provider.
- VM Isolation Robustness: Assurance needed regarding the robustness of VM-level isolation for security and performance.
Advertisement
 RF
RF








