Fog Computing Architecture and Operation Explained
Advertisement
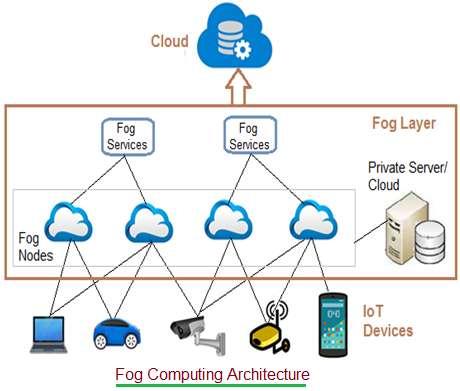
This article explains the fog computing architecture and how it operates. The architecture consists of three layers: IoT devices, the fog layer, and the cloud layer.
Introduction to Fog Computing
Fog computing, also known as edge computing, is a next-generation computing paradigm that extends cloud computing to the edge of the network. It addresses challenges associated with traditional cloud computing. The amount of data generated daily by IoT devices, sensors, and general internet usage is exploding. Estimates suggest around 50 billion devices will be online by 2020.
The existing cloud model struggles to handle this massive influx of data from private companies, factories, airplanes, healthcare devices, and more. Typically, IoT device data is sent to the cloud for analysis and storage. After analysis, the data is sent back to the devices or used to trigger actions. This process increases data bandwidth on the internet and introduces latency. Certain time-sensitive data cannot be handled efficiently by cloud networks due to this higher latency.

Figure 1 illustrates the three layers: device, fog, and cloud. The fog layer acts as an intermediary between the cloud and the devices that generate data.
Fog computing brings the cloud closer to the data sources, minimizing latency as fog nodes directly process data. It analyzes data generated by IoT devices. Key functions of the fog computing architecture include:
- Analyzing time-sensitive data at the network edge, where it’s generated. This reduces the volume of data sent to the cloud.
- Acting on IoT data within milliseconds based on defined policies.
- Sending only selected data to the cloud for long-term storage and in-depth analysis.
Fog Computing Architecture Components
The fog computing architecture uses both physical and logical elements (hardware and software) to implement an IoT network. As shown in Figure 2, it consists of:
- IoT devices
- Fog nodes
- Fog aggregation nodes
- Fog data services
- Remote cloud storage
- Local data storage server/cloud
Let’s examine these components in detail:
-
IoT Devices: These are devices connected to the IoT network using wired and wireless technologies. They generate vast amounts of data regularly. Various wireless technologies are used in IoT, including Zigbee, Z-Wave, RFID, 6LoWPAN, HART, NFC, Bluetooth, BLE, ISA-100.11A, etc. Common IoT protocols include IPv4, IPv6, MQTT, CoAP, XMPP, and AMQP.
-
Fog Nodes: Any device with computing, storage, and network connectivity can be a fog node. Multiple fog nodes are spread across a region to support end devices. These nodes are interconnected using different network topologies and can be located in various settings such as factory floors, power poles, railway tracks, vehicles, or oil rigs. Examples include switches, embedded servers, controllers, routers, and cameras. Highly sensitive data is processed at these nodes.
-
Fog Aggregate Nodes: Each fog node has an associated aggregate fog node that analyzes data within seconds or minutes. IoT data storage at these nodes can range from hours to days, covering a wider geographic area. Fog data services are implemented to support these aggregate node points, handling data of average sensitivity.
-
Remote Cloud: All aggregate fog nodes are connected to the cloud. Time-insensitive or less sensitive data is processed, analyzed, and stored in the cloud.
-
Local Server and Cloud: Often, fog computing architectures utilize private servers or clouds to store confidential company data. This local storage enhances data security and privacy.
Fog Computing Working Operation
Fog computing operates based on the type of data it receives: time-sensitive, less time-sensitive, or time-insensitive. Nearest fog nodes receive data input from the devices.
Here’s how it works:
-
Most Time-Sensitive Data: The nearest fog node to the device handles this data. After analysis, a decision or action is transmitted to the device. The fog node then sends a summary to the cloud for future analysis. Data analysis at the fog node happens in fractions of a second.
-
Less Time-Sensitive Data: This data is sent to an aggregate node for analysis. After analysis, the aggregate node sends a decision or action to the device through the nearest fog node. Aggregate fog nodes take seconds or minutes to complete the analysis and later send a report to the cloud for future reference.
-
Time-Insensitive Data: This data can wait for longer durations (hours, days, or weeks). It is sent to the cloud for storage and future analysis.
Advertisement
 RF
RF





